You have heard about quantum computing. It sounds like science fiction. Computers that harness the strange rules of subatomic physics. Machines that can solve problems in seconds that would take today's computers millions of years.
For most business leaders, quantum computing is a distant future problem. Something for the research labs at Google and IBM. Not something for next quarter's board meeting.
That assumption is dangerously wrong.
The timeline for quantum computers capable of breaking today's encryption is no longer decades away. Leading experts estimate that within 5 to 10 years, a cryptographically relevant quantum computer will exist. And here is the terrifying part: your encrypted data is being harvested right now, stored in the hope that tomorrow's quantum computer will decrypt it.
This is not a technical problem for your IT department. This is a governance problem for your board. And 2026 is the year you need a post-quantum cryptography roadmap.
Let me explain why.
The Problem That Most Boards Do Not Understand
Today's digital security rests on mathematical problems that are hard for classical computers to solve.
When you visit a bank website, your browser and the bank's server agree on an encryption key using something called elliptic curve cryptography. The math problem behind it is the elliptic curve discrete logarithm problem. A classical computer would take billions of years to solve it.
But a sufficiently powerful quantum computer running Shor's algorithm can solve that same problem in hours or minutes.
What breaks first:
1. Public key encryption (RSA, ECC, ElGamal)
2. Digital signatures (RSA signatures, ECDSA, DSA)
3. Key exchange algorithms (Diffie-Hellman, ECDH)
What survives (mostly):
1. Symmetric encryption (AES) with doubled key sizes
2. Hash functions (SHA-2, SHA-3) with larger output sizes
This means almost every secure communication your business relies on is vulnerable. Email. VPN connections. Software updates. Digital signatures on contracts. Secure file transfers. Authentication tokens. Everything.
The "Harvest Now, Decrypt Later" Nightmare
If you take nothing else from this article, understand this phrase: harvest now, decrypt later.
This is not a theoretical attack. It is happening right now.
How it works:
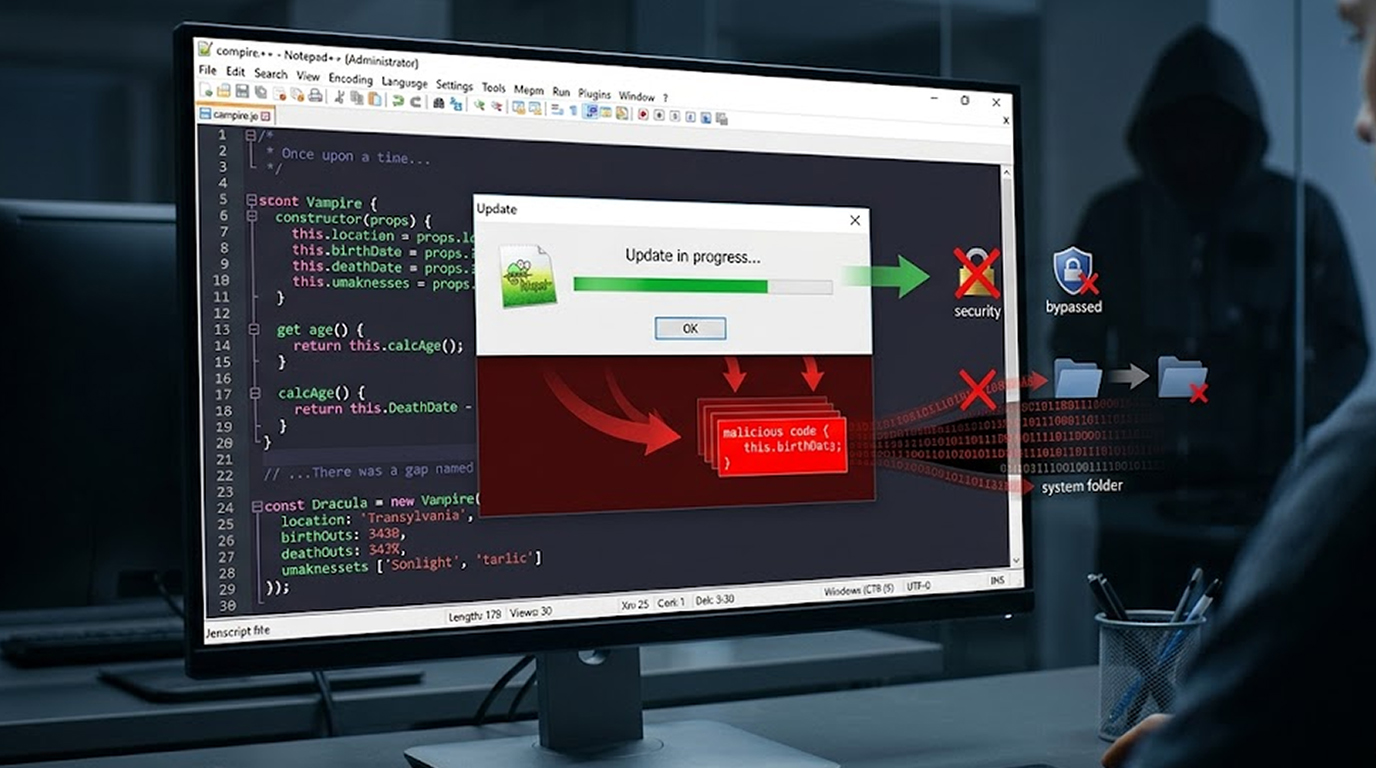
Step 1: An attacker intercepts and copies encrypted data as it travels across networks. They do not need to break the encryption today. They just need to store the encrypted data.
Step 2: The attacker waits. Perhaps 5 years. Perhaps 10 years. Eventually, a quantum computer becomes available.
Step 3: The attacker uses the quantum computer to decrypt everything they harvested years ago.
What data is at risk:
1. Financial records with 10-year retention requirements
2. Healthcare data that must be protected for decades
3. Trade secrets with long-term value
4. Legal documents and intellectual property
5. Government contracts and classified information
6. Customer personal data subject to privacy regulations
If your business stores sensitive data that must remain confidential for more than 5 years, that data is already vulnerable. Not because current encryption is weak. Because future quantum computers will break it.
Why 2026 Specifically?
The National Institute of Standards and Technology (NIST) has been running a multi-year process to select post-quantum cryptography algorithms. These are encryption methods designed to resist attacks from both classical and quantum computers.
The timeline is accelerating:
2022: NIST announced the first four selected algorithms
2024: NIST released draft standards for public comment
2025: Final standards published (FIPS 203, 204, 205)
2026: Organizations should begin migration planning
2027-2030: Critical systems should be migrated
2030+: Quantum risk becomes existential
The message from NIST and cybersecurity regulators is clear: 2026 is the year for planning. If your board has not yet discussed post-quantum cryptography, you are already behind.
The Board's Role: Governance, Not Technology
Board members are not expected to understand the mathematics of lattice-based cryptography. That is not your job.
Your job is to ask the right questions and ensure management is treating quantum risk with appropriate urgency.
Five questions every board should ask in 2026:
1. Do we have an inventory of all cryptographic assets?
You cannot protect what you do not know. Management should be able to list every place encryption is used: VPNs, web servers, email systems, databases, backup storage, code signing, authentication tokens.
2. What is our longest-lived sensitive data?
If you keep customer credit card data for 7 years for fraud analysis, that data is a candidate for harvest now, decrypt later. If you keep trade secrets for 20 years, that is an even larger risk.
3. Have we begun testing post-quantum cryptography?
Leading organizations are already running hybrid trials using both classical and post-quantum encryption in parallel. Your organization should at least be planning pilot programs.
4. Do we have cryptographic agility?
Cryptographic agility means your systems can swap out encryption algorithms without replacing entire applications. If your systems hard-code specific algorithms, migrating to post-quantum will be expensive and slow.
5. When will we complete migration for our most critical assets?
Your board should set a target date. 2030 is a reasonable deadline for most organizations. But financial services, defense contractors, and healthcare companies may need earlier timelines.
The Cost of Waiting
Every year you delay post-quantum planning increases your exposure and your migration cost.
Direct costs of waiting:
1. Larger accumulated data vulnerable to harvest now, decrypt later
2. More legacy systems to migrate
3. Less time to test and validate new algorithms
4. Potential regulatory penalties if quantum breaks compliance requirements
5. Competitive disadvantage as customers ask about quantum readiness
Indirect costs of waiting:
1. Loss of customer trust if a quantum breach occurs
2. Inability to bid on contracts requiring quantum-resistant encryption
3. Higher insurance premiums for cyber liability coverage
4. Auditor findings and regulatory scrutiny
Board members are trained to think about risk and return. Post-quantum risk is a high-impact, medium-probability risk. It belongs in your enterprise risk register today.
What a Post-Quantum Roadmap Looks Like
A proper post-quantum cryptography roadmap has four phases. The Board must anticipate being presented with a presentation of the Management Plan for these phases that is organized by defined timelines and budgets.
Phase 1: Discovery and Inventory (2026)
Objective: To understand what exists and how to approach resolving it.
Deliverables:
1. An inventory will document the company's entire encryption usage across the enterprise.
2. Systems will be ranked based on their data sensitivity and age.
3. An assessment will evaluate the enterprise's current state of crypto-agility.
4. Dependencies on vendors will be identified (for example, do your cloud computing providers support post-quantum encryption? Do your software providers support post-quantum?).
Board Action: Inventory received, criteria for prioritization of inventory approved, budget for Discovery approved.
Phase 2: Standards & Testing (2026-2027)
Objective: To establish a framework for transitioning to quantum safe methods of cryptography by way of non-mission critical systems.
Deliverables:
1. To develop proposed internal standards for evaluating post quantum encryption algorithm choices
2. To create a testing environment using existing classical and quantum encryption algorithms and combinations thereof.
3. To execute a pilot implementation of post quantum technology on at least one low-risk non-mission critical system.
4. To define a benchmark to measure performance of post quantum cryptographic algorithms that utilize larger key sizes and longer signatures.
Board Action: Review results of pilot implementations to Approve addition of additional post quantum cryptographic implementations to higher-risk mission critical applications and monitor vendors' plans (roadmap, etc.) regarding post-quantum cryptographic implementations.
Phase 3: Migration of Mission Critical Systems (2027-2029)
Objective: To protect sensitive mission critical data with long retention periods.
Deliverables:
1. All systems processing data that have a retention period greater than 10 years will be migrated
2. All services that are publicly facing (e.g. web, email, and virtual private networks) will be migrated
3. "Post-quantum" digital signatures will be implemented for software updates
4. Incident response plans will be revised for quantum-specific scenarios
Board action: Quarterly review of the status of migrations and to approve any delays and exceptions to the plan, as well as notify customers and regulators.
Phase 4: Complete Migration of All Systems and Continuous Enhancement/Improvement of All Systems 2029 - 2031
Objective: All System's Complete Migration and Continuing Governance of Cryptographic Technologies.
Deliverables:
1. All Enterprise Systems with post-quantum Encryption.
2. A Program of Governance for all Current and Future Issued Public-Key Encryption Algorithms and Public-Key Encryption Algorithms.
3. Periodic Testing for Validation Against Quantum Attacks of the Effectiveness of Post-Quantum Encryptions.
4. Participation with Other Companies in Creating Post-Quantum Working Groups.
Board Action: Report to the Board with Attestation of Company’s Quantum Preparedness by the End Of each Fiscal Year and provide regular updates to overall Cyber Security Report.
Using A Hybrid Approach: Neither All or Nothing Can Be Expected
A common misconception is that Companies have to choose between classical and post-quantum salts. That is false.
The recommended approach is hybrid cryptography. Use both classical and post-quantum algorithms together. A message is encrypted with both. An attacker must break both to read the message.
Advantages of hybrid:
1. Backward compatibility with existing systems
2. Protection even if post-quantum algorithms have unknown weaknesses
3. Smooth transition path
4. Defense in depth
Most major technology vendors are implementing hybrid approaches. Cloud providers like AWS, Azure, and Google Cloud have announced post-quantum options for their services. Your roadmap should leverage these vendor capabilities rather than building from scratch.
Industry-Specific Timelines
Different industries face different levels of quantum risk. Your board should understand where your industry falls.
Financial Services (Highest urgency)
Banks process transactions that must remain secure for decades. Wire transfers, mortgage records, and trading data are prime targets for harvest now, decrypt later. Regulators are already asking about quantum preparedness. Target migration: 2027-2028.
Healthcare (High urgency)
Medical records must stay confidential for 50 years or more under some regulations. A quantum computer in 2035 could decrypt patient records from 2025. Target migration: 2028-2029.
Defense and Government (Highest urgency)
Classified information has indefinite confidentiality requirements. Nation-state adversaries are certainly harvesting encrypted government communications today. Target migration: 2026-2027.
Technology and SaaS (Medium urgency)
Cloud providers and software companies need to protect customer data and their own intellectual property As early adopters, they will have a competitive advantage over later adopters. Target migration: 2028-2030.
Manufacturing and Energy (Medium urgency)
Industrial control systems have long lifespans. A power plant built today will operate for 30 years. Upgrading cryptography on embedded systems is difficult. Plan early. Target migration: 2028-2030.
Retail and Consumer Goods (Lower urgency)
Credit card data has shorter retention requirements. But customer loyalty data and business partner communications still need protection. Target migration: 2029-2031.
What Happens If You Do Nothing
Let me paint a clear picture of the downside.
Scenario: No board action in 2026
2026: No action is taken by your Board regarding post-quantum planning. Your organization continues with classical encryption, and your IT department has heard about quantum-resistant cryptography but neither the budget or mandate to proceed with any action has been provided.
2028: A competing organization announces they have become compliant with post-quantum cryptography in their annual report. Your customers ask when your organization will be compliant, and you do not have a response.
2029: A regulatory authority issues updated guidance requiring financial institutions to have a post-quantum migration plan. Your organization is forced to develop a plan to comply, only to learn that your current core banking platform will require a complete rewrite out of necessity to use new encryption algorithms.
2031: The first relevant quantum computer is developed and while it cannot be used for widespread attacks at this stage, you can see where the industry is headed.
2033: Your organization begins the emergency migration. Your costs are five times what they would have been if you had properly scheduled this migration. Many of your critical applications are unable to carry out the migration due to API compatibility, exposing your customer data to possible alternative sources.
2035: Quantum computing is commercially available. Your previous backups are unencrypted due to the new quantum nature of the encryption algorithms. As a result, all of your customer data from 2020 through 2030 are now publicly available.
The delays enumerated above are not simply scare tactics; this is what will happen with your organization if you continue to put off defining a plan for your organization to be post-quantum compliant.
The Benefits of Acting Early
Let me demonstrate the benefit of acting early.
Example: Your Board supports a post-quantum roadmap by 2026
Your company has identified quantum preparedness as a strategic goal.
2027: You will have successfully conducted pilot projects. Your marketing department will tout your company's quantum-safe security in their customer communications.
2028: Your company wins a contract from a competitor due to your use of quantum-safe encryption.
2029: Government regulators issue their guidance. Your business is compliant. Competitors are scrambling to catch up.
2031: The first working quantum computer is shown to the world, and customers start seeing news articles about it and want to know how safe their data will be. You will be able to say, “Yes,” and your competition won’t be able to.
2033: You finish migrating to your new systems. You successfully spent your budget over 7 years. Competitors spent an emergency budget over 2 years. You will take share from them.
Using post-quantum cryptography early on is a way to minimize your risk and will give you an advantage over your competitors.
How to Get Started Today
Your board does not need to become expert in lattice-based cryptography. You need to ask for a plan.
Immediate actions for your next board meeting:
1. Add quantum risk to the agenda
Put post-quantum cryptography on the formal agenda for your next meeting. This signals to management that the board takes the issue seriously.
2. Request a quantum risk assessment
Ask your CISO or CIO to prepare a briefing on quantum risk. Request: timeline estimates, inventory of sensitive long-lived data, assessment of current cryptographic agility, and preliminary budget estimates.
3. Ask about vendor readiness
Request a summary of post-quantum roadmaps from your major technology vendors. Cloud providers. Software vendors. Hardware manufacturers. If they are not planning for post-quantum, consider alternatives.
4. Examination of retention policy of data
Should customer data stay with us for 10 years and should we anonymize or delete some of the older datasets? A quick way to mitigate quantum risks is through a reduction in retained data.
5. Target completion date for roadmap
Management should agree to approve the post-quantum roadmap no later than 2026, providing them with a certain timeframe to prepare recommendation documentation.
Conclusion: 2026 Is the Year of Planning
You have time. The first quantum computer that can break RSA is not here yet. But the planning window is closing.
Every year you delay makes the eventual migration harder, more expensive, and more risky. Your encrypted data is already being harvested. Your competitors are already planning. Your regulators are already watching.
The board's job is to govern risk and seize opportunity. Post-quantum cryptography is both. It is a risk your organization will face. It is an opportunity to demonstrate leadership.
Approve the roadmap in 2026. Thank yourself in 2031.
FAQ Section
1. When exactly will quantum computers break today's encryption?
Most experts estimate a cryptographically relevant quantum computer will exist within 5 to 10 years, but exact timing is uncertain. The risk is not a single date but a gradually increasing probability. The key point is that encrypted data harvested today can be decrypted later, so planning must happen before the quantum computer exists.
2. What is a post-quantum cryptography roadmap board members need to approve?
A post-quantum cryptography roadmap is a multi-year plan for migrating an organization's encryption from classical algorithms (like RSA and ECC) to quantum-resistant algorithms (like those selected by NIST). The roadmap includes discovery, testing, critical system migration, and full migration phases with specific timelines and budgets.
3. What does "harvest now, decrypt later" mean for my business?
Harvest now, decrypt later means attackers are copying and storing your encrypted data today, waiting for quantum computers to decrypt it in the future. Any sensitive data with a long confidentiality requirement (financial records, healthcare data, trade secrets) is vulnerable. If your business keeps customer data for 7+ years, that data is at risk.
4. Is post-quantum cryptography currently reliable and practical for enterprises?
Yes. NIST has issued its final post-quantum cryptography standards for use in 2024 and 2025. Many major cloud providers and technology vendors now provide post-quantum solutions today. During the transition period, using both classic and post-quantum algorithms is the best approach (hybrid).
5. What are the consequences of no longer having my board approve the post-quantum roadmap by 2026?
If your organization does not approve a post-quantum strategy soon, your organization will become subject to harvest now/decrypt later risks. Your enterprise may also incur additional migration costs if legacy systems become more entrenched. You could also risk doing business with both competitors or regulators. Lastly, your organization may not be eligible to bid on contracts requiring quantum-resistance security features.