PHANTOMPULSE RAT is a newly developed and highly advanced Remote Access Trojan (RAT) that is getting a lot of attention within the cybersecurity community in 2026. The backdoor is based on the .NET Framework and was previously undocumented. The malware also has advanced command-and-control (C2) capabilities operating in undetected fashion while also showing development indicators that suggest that AI may have played a significant role in its creation.
PHANTOMPULSE RAT was delivered via the popular note-taking app, Obsidian, which has been leveraged by an attacker to gain access to its target (users working in finance and cryptocurrency). The release of this RAT demonstrates how attackers are abusing commonly used productivity applications to obtain initial access to a victim's computer.
This article explains what PHANTOMPULSE RAT is, how it infects a target's computer, its ability to carry out a range of functions, as well as how organizations and individuals can protect themselves from this type of malware.
What Is PHANTOMPULSE RAT?
Quick Security Checklist
- Scan your system or website
- Update all dependencies
- Change passwords
- Enable 2FA
PHANTOMPULSE RAT is a fully featured Remote Access Trojan for Microsoft Windows computers developed mostly in .NET (C#). The initial recognition of PHANTOMPULSE RAT happened in early April of 2026 during a campaign referred to as REF6598, by Elastic Security Labs.
Here's what's so interesting about this backdoor:
1. As it stands, this backdoor was developed using the tools of AI (language models). The various instances of verbose and reflective debug strings (i.e., [Step 1],[Step 1/3]) that appear in the code suggest that it was created using a large language model.
2. The stealth techniques of PhantomPulse (i.e., backdoor) utilize various methods to evade detection from standard antivirus programs. Examples of stealth techniques include loading modules reflectively, using module stomping, and executing directly in memory to inject into a process.
3. The advanced attributes of PHANTOMPULSE as an advanced backdoor are demonstrated through its ability to establish an Ethereum blockchain-based command-and-control server from Ethereum transactions.
PHANTOMPULSE will not serve as a standard, low-cost/commodity RAT (remote access Trojan) and is designed to operate specifically against high-value targets that have significant quantities of sensitive financial assets or cryptocurrency assets.
How PHANTOMPULSE RAT Spreads: The Obsidian Plugin Abuse Chain
The infection starts with social engineering rather than zero-day exploits:
1. Using a fake identity as a venture capital firm contact through LinkedIn, attackers will reach out to potential victims.
2. They will then transition conversations to a Telegram group that includes false “partners.”
3. When these victims receive an invitation and the Vault has been shared among all users (including victim) with access to the malicious Obsidian Community Plugin, they will open it.
4. Once the Vault has been opened by the victim, and after being compelled by the attacker to activate Community Plugin(s), malicious PowerShell scripts are executed with the Shell Commands Community Plugin with no user interaction.
On Windows, this chain downloads a custom loader called PHANTOMPULL, which decrypts and reflectively loads the final PHANTOMPULSE RAT payload entirely in memory. The loader uses AES-256-CBC encryption and includes anti-analysis techniques.
A similar but distinct chain targets macOS using obfuscated AppleScript and LaunchAgent persistence.
Obsidian has proven to be a legitimate tool for professionals in technology and finance. This way of delivering is an effective method.
PHANTOMPULSE RAT Overview
PHANTOMPULSE RAT will allow an Attack to achieve complete control over the Target Host.
Functionalities:
1. System Information : Gather information regarding the hardware and software of the host, as well as network information.
2. Keystrokes : Capture all Keystrokes to steal user credentials.
3. Screenshots : Capture periodic or on-demand screenshots of the host computer.
4. File Upload/Download : Exfiltrate sensitive files or download tools from the attacked host to the attacker’s machine.
5. Process Injection : Use various advanced techniques of terminating processes to activate stealthy processes.
6. Command Execution : Execute arbitrary commands from the Command and Control (C2) server.
7. Persistence Methods : Use known or defined persistence methods to provide a remotely accessible point of entry into the host computer on each reboot.
The PHANTOMPULSE RAT communicates via the WinHTTP protocol and supports both normal fall-back C2 infrastructure. The operator will receive telemetry data, and the RAT will receive commands via the C2 to execute specific actions or exfiltrate data.
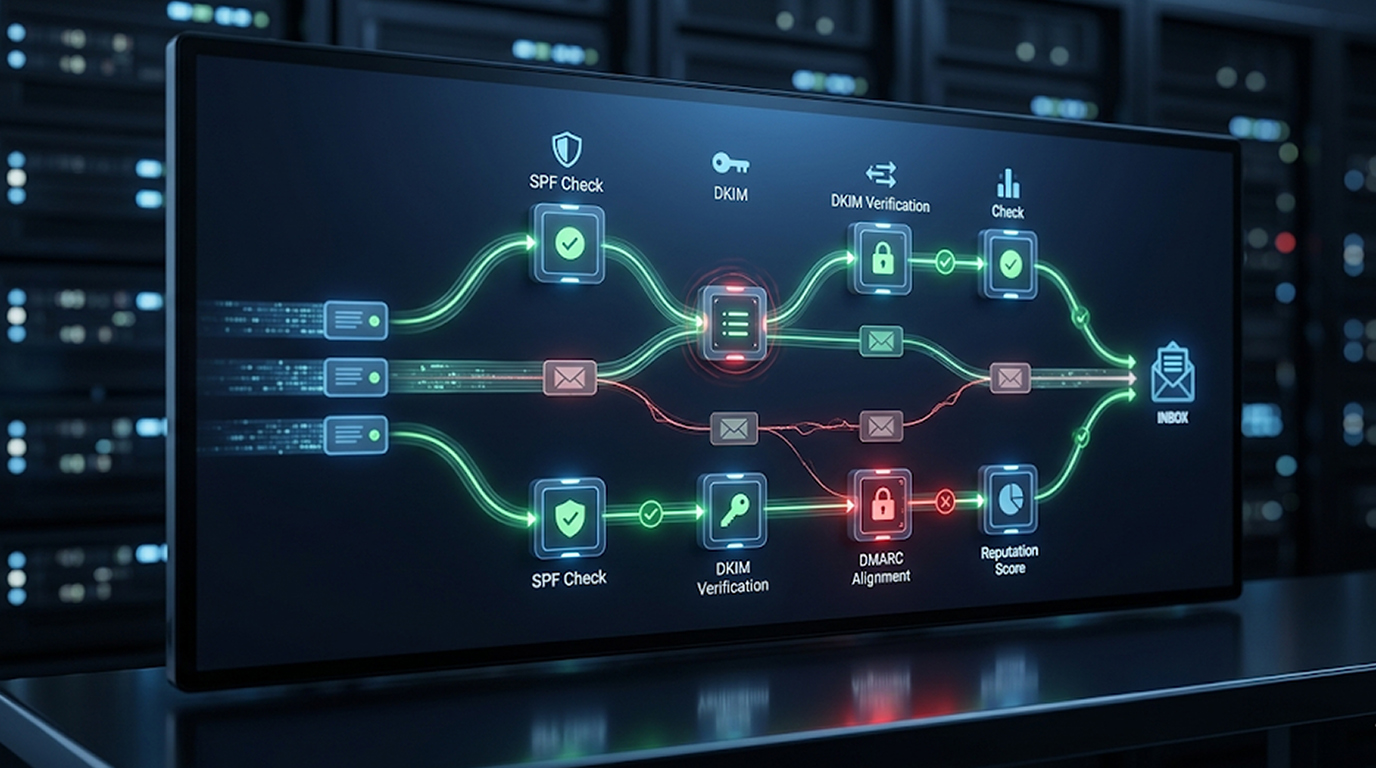
The Ethereum Blockchain C2 Technique
PHANTOMPULSE RAT's implementation of the Ethereum blockchain to identify the location of its C2 addresses is innovative. Each instance of PHANTOMPULSE RAT has a predefined Ethereum wallet address. By using public explorer sites such as Etherscan to search for the most recent transaction associated with this hard-coded Ethereum wallet address, a user can retrieve the C2 address that is embedded in the transaction.
This “drop” strategy makes it difficult to block traditional C2 methods of controlling the RAT, as the address of the C2 can be modified dynamically without any changes being made to the executable binary on the RAT. The RAT also has the effect of mixing malicious traffic with legitimate blockchain queries.
Why PHANTOMPULSE RAT Is Gaining Traction in 2026
There are many reasons why PHANTOMPULSE RAT is becoming more prevalent:
1. Targeting High-Value Targets : Finance & crypto professionals tend to be perfect targets to compromise since they will usually have access to very high-value accounts.
2. Living off The Land : Heavy use of legitimate tools (e.g., Obsidan, PowerShell, blockchain queries from web browsers) will minimize the footprint of the malware.
3. AI-Generated Code : Faster development cycles will lead to faster iterations of more polished & less bug-prone code (i.e., another way of saying code is Less bug infested than earlier versions).
4. Cross Platform Elements : Although the primary RAT is for Windows, macOS has also been exploited; thus, the target surface area is much larger.
According to cybersecurity experts, the emergence of PHANTOMPULSE indicates a growing trend towards the use of more resistant and blockchain aware malware designed to bypass the latest rate of detection.
How to Detect and Protect Against PHANTOMPULSE RAT
Detection Indicators
There are a number of indicators to watch for when looking for PHANTOMPULSE RAT.
1. Child process spawned from Obsidan.exe that behave abnormally
2. PowerShell command execution is occurring uncommonly and/or has been base64 encoded
3. Specific mutexes have been created (e.g., hVNBUORXNiFLhYYh)
4. You are seeing outbound connections to suspicious domains or to a blockchain explorer followed by a connection to the Command and Control server (C2).
5. PHANTOMPULL loader artifacts or reflective DLL loading will be on the system.
Protection Best Practices
1. Be extremely cautious with shared Obsidian vaults from untrusted sources.
2. Automatic Plugin execution and Community Plugins must be turned off unless they are really needed.
3. Prevent the Obsidian app from making PowerShell calls or downloading executable files by using application whitelisting.
4. Monitor for any unusual blockchain related traffic to/from any endpoints on your network.
5. Deploy sophisticated endpoint detection & response (EDR) capabilities capable of behavioral analytics against endpoints.
6. Regularly update both Obsidian and installed plug-ins, and check the community plug-ins frequently.
7. Provide rigorous social engineering training, especially for finance and crypto teams.
Organizations that are hunting for the specific YARA rules published by the Elastic Security Labs can help them discover infections quickly.
The Future of Stealth Backdoors Such as PHANTOMPULSE
The PHANTOMPULSE RAT shows how bad actors are leveraging social engineering, legitimate productivity tools, AI assisted development and blockchain technology to create persistent malware. Growing use cases for collaborative and note-taking applications in enterprises drive the exponential growth of exploitation of those types of application plugin/environments.
As a result, organizations will need to revise their methods for protecting themselves from these new types of threats by reducing their use of signature-based detection mechanisms and increasing their use of behavioral monitoring mechanisms and zero trust models for accessing third-party applications.
Conclusion
The PHANTOMPULSE RAT showcases how the evolving threat landscape in 2026 has changed to include stealthy, innovative methods that are specifically designed to evade traditional cybersecurity measures. It is extremely capable of wreaking havoc on organizations in specific industry sectors. This is due to the threats architecture being based on .NET as well as its use of an Ethereum C2 mechanism along with its ability to deliver through Obsidian.
By understanding how this backdoor operates and implementing strong procedural and technical controls, security teams and individuals can reduce the risk of falling victim to similar advanced persistent threats.
FAQ Section
Q1: Can you tell me if you know the PHANTOM PULSE RAT?
PHANTOM PULSE RAT stands for Remote Access Trojan Remote Access Trojan (RAT). This new remote access trojan is built on software based on the .NET platform. The PHANTOM PULSE RAT was developed in 2026 and possesses some advanced stealth abilities. The PHANTOM PULSE RAT is delivered via malicious Obsidian plugin exploits and includes features such as; keylogging, process injection and use of the blockchain to communicate back to the C2 (Command and Control) server.
Q2: How does PHANTOM PULSE RAT find its C2 (Command and Control) connection to the Ethereum blockchain?
Once the PHANTOM PULSE RAT needs to connect to its C2 (Command and Control) server it will look up its command and control (C2) address in the blockchain. To get the current C2 address on the blockchain, the RAT queries a hardcoded Ethereum wallet for the most recent transaction made to both a specified from and to address. Because the C2 address will constantly change dynamically, blocking it is likely to be a very difficult task.
Q3: Is PHANTOM PULSE RAT only for Microsoft Windows?
The PHANTOM PULSE RAT payload is Windows focused; however, the REF6598 campaign also includes a macOS infection chain consisting of AppleScript and LaunchAgent persistence which makes this a cross platform attack.
Q4: Is there AI used within the PHANTOM PULSE RAT?
The PHANTOM PULSE RAT binary contains verbose structured debugging output which uses step-by-step numbering as characteristic of either code created entirely by AI coding or code created through extensive assistance by large language models.
Q5: How can I defend myself against PHANTOMPULSE RAT?
Do not open shared Obsidian vaults from sources that you do not know, disable unneeded community plugins, use EDR solutions with strong behavioral detection capabilities and train staff to recognize social engineering attempts using LinkedIn and Telegram that may be sophisticated.