email spoofing techniques
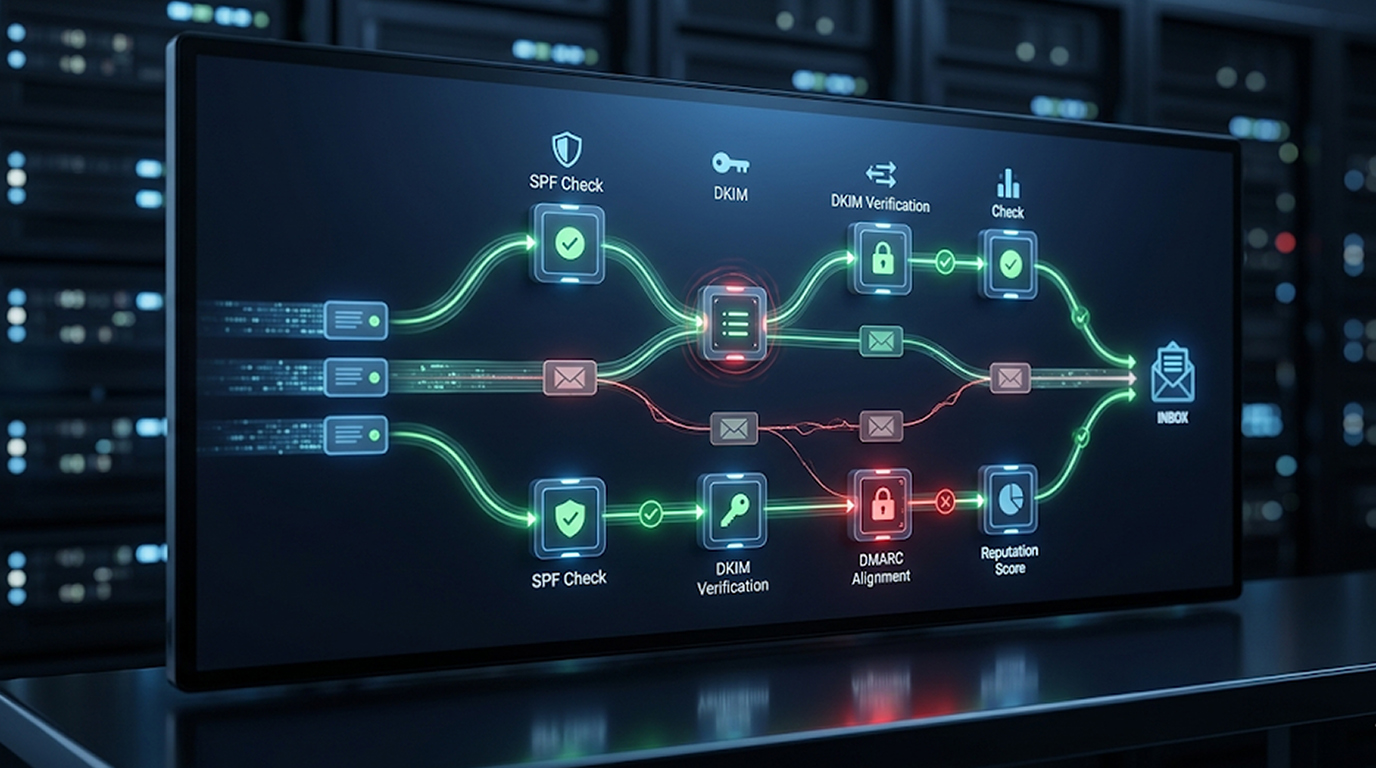
While there has been a significant improvement in the use of SPF, DKIM, and DMARC, sophisticated methods for email spoofing are still able to succeed in 2026 by attacking any of the following areas: misconfiguration, protocol limitations, and human psychology. Attackers will create spoofed phishing emails that look to be legitimate by exploiting these weaknesses.
These protocols do a great job of mitigating domain spoofing, but they are not completely effective at doing this. Understanding these remaining gaps can help defense organizations increase their email security and train their users effectively.
This guide will provide in-depth analysis of the most effective forms of email spoofing that are still effective today using examples from real-life scenarios.
Why SPF, DKIM and DMARC Cannot Stop All Spoofing
SPF checks the sending IP addresses, DKIM ensures that the data sent with the email matches the data on the sender's computer using a digital signature, and DMARC ties the two together through alignment checking and policy enforcement, but each protocol has its gaps.
1. Many domains are still using a DMARC policy of p=none (monitor only).
2. Protecting subdomains is lacking for many domains.
3. The protocols focus on the domain but not on the visible display name.
4. Email routing and third-party services have many opportunities for bypassing the protocols.
Attackers typically combine technical exploits along with social engineering techniques to maximise their success.
Technique 1: Spoofing Display Names (The Most Common Bypass)
Spoofing display names only affects how a person sees the sender instead of using the actual email address used.
The way this works is:
1. When a person receives an email their display name may read “CEO John Smith” or “PayPal Support”
2. The "From" address could have been set to an address that looks like but is not the same as the address through which the email was sent (e.g., john.smith@paypa1-support.com).
3. If the sender used SPF, DKIM, and DMARC to authenticate his domain then those authentication methods will show "pas" since the sender was spoofing the display name.
This method works well on mobile phones because many mobile email applications do not show users the "From" address and show only the display name. This method also does not have any type of technical check applied to it and relies solely upon user trust.
Example: When user opens email and displays "From: HR Department " the true "From" address is hr-dept@yourcompany-support.net.
Technique 2: Domain Spoofing: Lookalike/Cousin Domain Attacks
Hackers have registered domains that look similar visually (typosquatting or homoglyphs) with their own SPF/DKIM and DMARC registrations … as well as other common examples such as:
1. Heterographs (Cyrillic ‘а’ for example, instead of an ASCII ‘a’)
2. Extra words or numbers added (example: yourcompany-support.com)
3. A new gTLD that mimics the original
Because these domains have valid authenticating information (SPF/DKIM/DMARC) from either the domain registrant or hosting service, all subsequent emails sent from those domains are accepted. DMARC only provides protection for the precise domain that was published. Therefore, any of the above types of similarly reconstructed domains would not be provided due to the lack of a corresponding DMARC record.
Additionally, the use of artificial intelligence (AI) applications has made it possible for criminals to quickly create and produce convincing content and visuals that look identical to legitimate domains.
Technique 3: Utilization of Microsoft Direct Send & Internal Routing Abuse
MS Office 365's Direct Send feature allows applications and devices to send email without fully authenticating to Microsoft Office 365. Malicious actors have leveraged this feature by creating a specially designed message with the From & To address using an internal address (sometimes even the same one). Because both addresses appear to be internal, emails sent this way are able to impersonate internal communications, thus circumventing external attempts at spoof protection (e.g., DMARC at p=reject) and third-party secure email gateways.
Even with DMARC set to p=reject, misconfigured tenants or complex routing scenarios are able to allow the email to land in inboxes, typically with accompanying QR code lures or malicious attachments.
Technique 4: Subdomain Configuration & Hijacking
While most organizations have security measures for their maindomain, such as registrars, many do not have similar measures in place regarding their subdomains.
Techniques of Attack are:
1. Subdomain takeover (aka, dangling DNS ~ records, expired services (ex. AWS, AZURE, HEROKU))
2. Attacker claims the current subdomain to then publish their own SPF / DKIM / DMARC records.
3. An email originated from a compromised subdomain will inherit trust from the parent brand.
This allows fully authenticated spoofing that passes all three protocols for that subdomain.
Technique 5: Forwarding and Sender Rewriting Scheme (SRS) Exploitation
Email forwarding can break SPF alignment. Some systems use Sender Rewriting Scheme (SRS) to fix this, but it can be abused in certain routing chains.
If a hacker fakes a message, passes it through a mail platform that will alter the sender's information, and then delivers that last email as though it has passed SPF and DMARC authentication, even though the actual original has been spoofed.
Complex enterprise routing setups (especially in Microsoft 365 with third-party connectors) amplify this risk.
Technique 6: Trusted Infrastructure and Vendor Compromise
Attackers compromise or abuse trusted third-party sending services, marketing platforms, or compromised vendor accounts that already have valid SPF/DKIM/DMARC for the target domain.
Because the email comes from authorized infrastructure, authentication passes. The spoofing happens through legitimate (but abused) channels.
How to Protect Against Modern Email Spoofing Techniques
No single protocol stops every attack.
Layering your defenses consists of the following:
1. Demonstrate strong DMARC adherence: Require your DMARC to be p=quarantine or p=reject instead of p=none. Use wildcard policies when possible to protect subdomains.
2. Regularly monitor your DMARC reports to identify any unauthorized senders/misconfigurations.
3. Train users: Users should always verify the email address they received vs. the proposed sender display name; for example, soliciting sensitive information with urgency and using official communication methods for verification.
4. Use email security technology. Incorporate behavioral analysis, A. I., and gateways to analyze mail beyond simple authenticated users.
5. Disable any services that pose a risks. Review/limit the number of direct sending connections you’ve purchased (i.e., Microsoft Direct Send) wherever possible.
6. Make sure to perform regular audits of your DNS and eliminate all dangling records.
7. Implement other control mechanisms (My F.A.C.E.), create a password manager, and provide endpoint protection (e.g., Antivirus, etc).
Utilizing automated solutions to monitor and report DMARC compliance along with branding spoofing in email will increase your organization’s visibility into this strategy.
The Future of Email Spoofing in 2026 and Beyond
With the widespread use of artificial intelligence in spoofing, the delivery of fraudulently created email spoofed messages is much more realistic, personalized, and difficult to arrange for users than ever before. Meanwhile, leading service providers continue to tighten requirements for creating accounts that send out legitimate email, creating new opportunities for attackers to spoof emails based on insufficiently configured or adopted technology.
The best way to defend against email spoofing is by implementing strong technical controls (e.g., full DMARC enforcement), including ongoing education for users about how email spoofing works and how to detect suspicious emails.
As long as there are technical vulnerabilities and human factors (e.g., human error), spoofed email techniques that can circumvent SPF, DKIM, or DMARC will continue to present a danger in 2026. For instance, spoofed email delivery using lookalike domains, routing errors, and subdomain issues will continue to be successful against organizations with inadequate protections.
Conclusion
To reduce your risk of being conned by a spoofed email, you should strictly enforce your DMARC policy, monitor your DMARC reports, secure your subdomains, and train your employees to look beyond the display name when receiving an email. Email authentication is critical, but it has to be part of a well-equipped, layered security strategy that addresses the whole email delivery lifecycle, including prevention, detection, and response.
Be proactive, take the time today to review your DMARC posture and educate your employees about identifying the latest spoofed email techniques.
FAQ Section
Q1: Is it possible for attackers to spoof email with SPF, DKIM, or DMARC?
Yes. If these protocols are enforced correctly, they will block spoofing of domains directly. However, there are still many methods that attackers can use to spoof email but not be detected, such as display name spoofing, lookalike domains, or misconfiguring routes.
Q2: Does DMARC at p=reject block email spoofing?
This protection is strong against spoofing of a given domain, but does not in any way block display name spoofing, lookalike domains, or abuse by trusted third parties, all of which can also be used to spoof email.
Q3: What is display name spoofing?
An example of display name spoofing would be if a person forged the display name "CEO" but used a different email address. This type of forgery does not check the actual domain, so it bypasses any of the authentication protocols.
Q4: How can subdomain hijacking be used for email spoofing?
Attackers use dangling DNS records to take over subdomains that are not in use and send authenticated email that appears to come from the trusted parent brand. As a result, they pass SPF, DKIM, and DMARC checks as well.
Q5: What is the best method for preventing email spoofing in 2026?
The best method for preventing email spoofing in 2026 would be to enforce DMARC with a p=reject policy, monitor reports on email delivery, protect all subdomains, disable risky functions like Direct Send where the feature is available, provide user education, and utilize advanced behavior-based email security tools combined with DMARC at p=reject to provide additional protection.