ZionSiphon malware is a specialized Operational Technology (OT) malware designed to sabotage water treatment and desalination facilities According to a report by cyber security company Darktrace released in April 2026 on ZionSiphon malware, the malware had been analyzed and disclosed to the public by Darktrace. ZionSiphon malware has demonstrated its political motivations and attempts to disrupt critical infrastructure.
ZionSiphon malware does not behave or conduct itself like traditional ransomware or data stealing malware but focuses on causing physical damage to the infrastructure by manipulating key parameters such as chlorine levels and hydraulic pressure in water systems.
What Is ZionSiphon Malware?
ZionSiphon is a malware for Windows operating systems that utilizes conventional IT practices but can also utilize advanced techniques to attack Industrial Control System (ICS) or Operational Technology (OT) environments.
The following are key features of ZionSiphon malware:
1. Geographic Targeting: ZionSiphon malware contains hard-coded IPv4 address ranges for specific geographic locations that only target devices connected to the Internet of Things (IoT) in the country of Israel.
2. Sabotage Functionality: ZionSiphon malware has built-in functions (e.g. IncreaseChlorineLevel()) that will seek out and alter ONLY those configuration files that are related to a desalination plant, reverse osmosis, chlorination, or water pressure control.
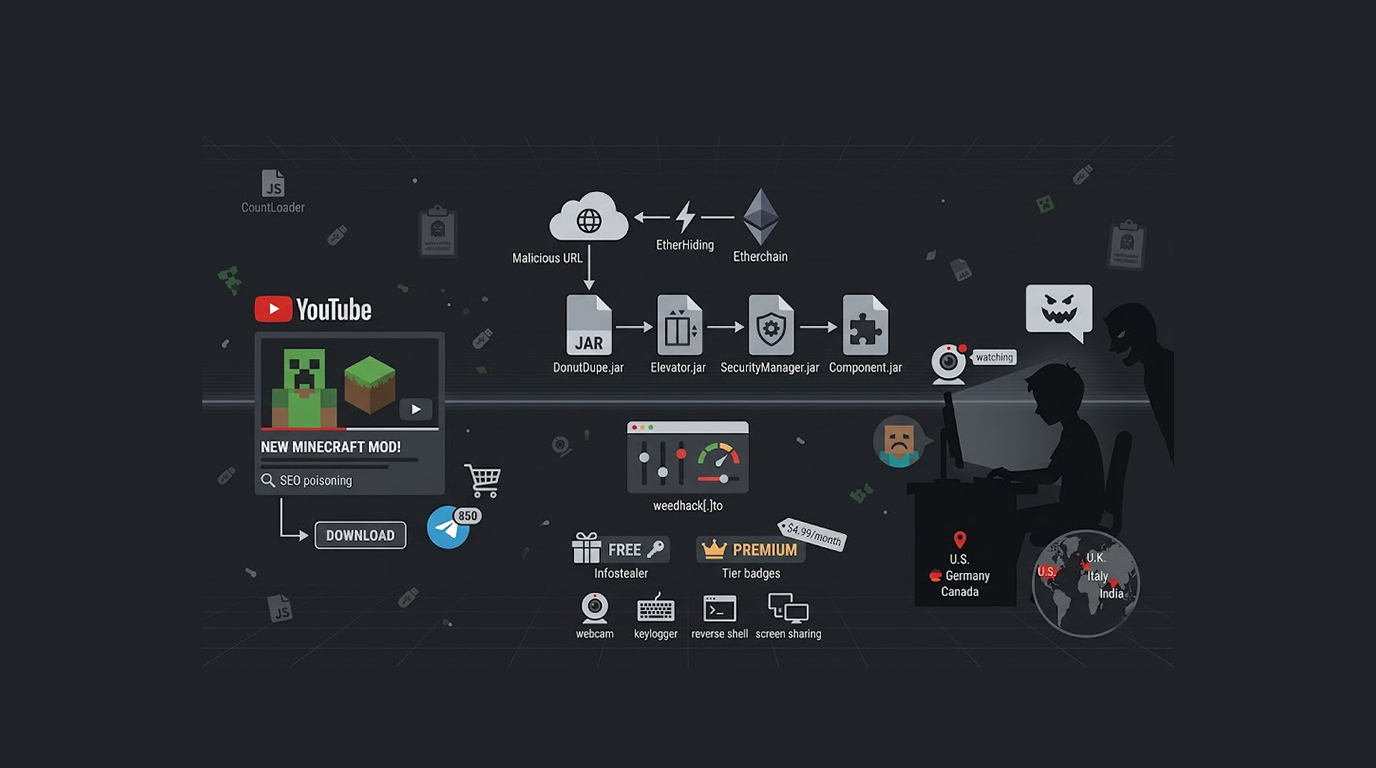
3. Propagation: The ZionSiphon malware mainly spreads through the infection of USB flash drives. Once it infects a drive, it is able to spread to local computers and other USB flash drives.
4. Persistence: ZionSiphon malware uses registry keys to maintain persistence within Windows and can also use techniques to hide its presence by mimicking legitimate Windows processes such as svchost.exe.
5. Development Stage: The sample that was analyzed appears to have been a pre-release (developmental) or a partially “defanged” version of ZionSiphon, containing several significant code errors that prevented the malware from being fully activated.
ZionSiphon malware includes strings of text suggesting that the malware intends to do harm to Tel Aviv and Haifa's residents; therefore, the malware is of a political or hacktivist origin.
Why Was ZionSiphon Malware Discovered by Darktrace?
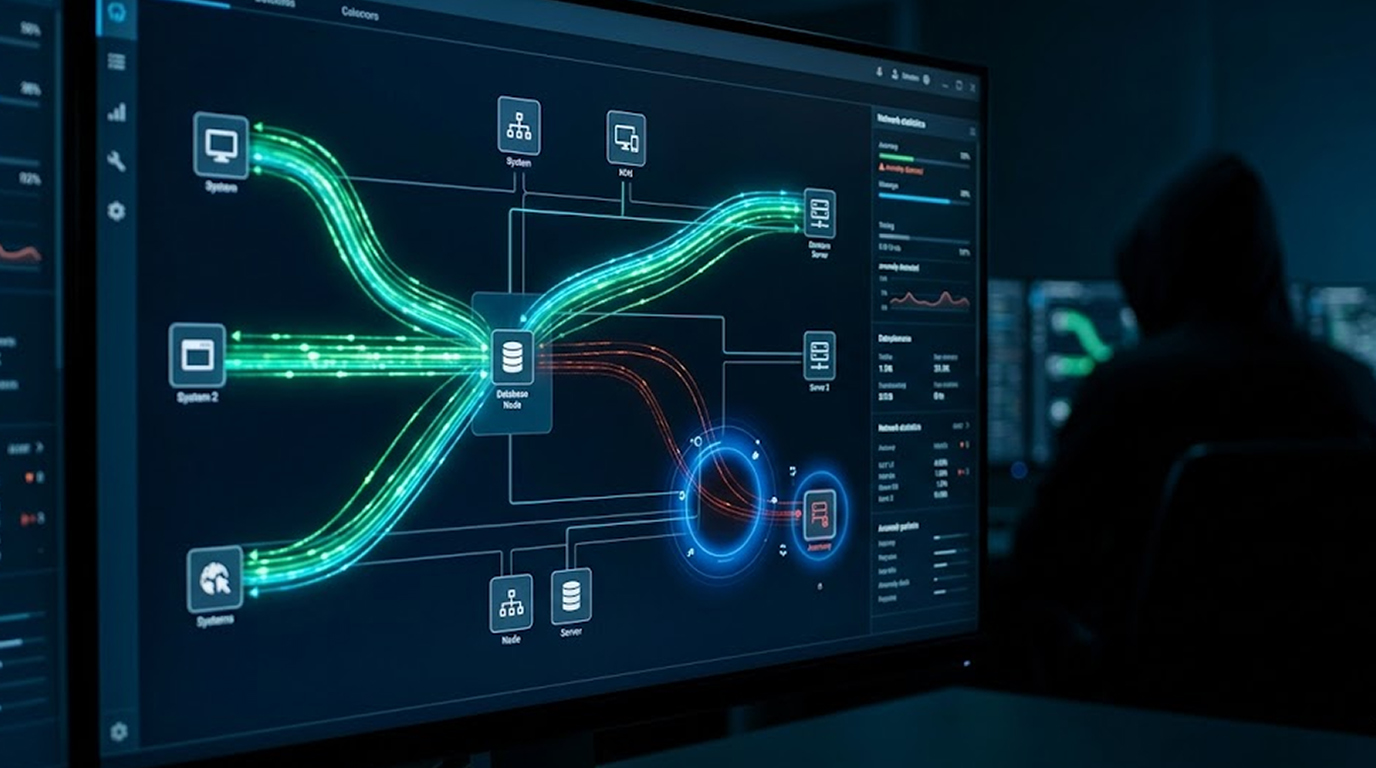
Darktrace is a leader in behavioral threat detection (via AI) and made a discovery through its normal methods monitoring for anomalous activity on client systems as well as through threat intelligence.
Darktrace identified the activity of ZionSiphon malware through its sophisticated AI technology due to the following peculiarities associated with the behavior of ZionSiphon:
1. The presence of numerous suspicious USB activities, and attempts to access OT configuration files.
2. Numerous occasions of abnormal scanning behavior for industrial protocols, such as Modbus, DNP3 and S7comm.
3. IT propagation techniques combined with OT-specific sabotage logic were going to attract significant attention as highly anomalous.
In April of 2026, Darktrace published an extensive technical report called “Inside ZionSiphon,” outlining the malware’s capabilities and known targets, as well as how it was designed.
Their approach of assessing behavioral AI allowed Darktrace to identify the malware even though the sample’s construction contained errors that would likely prevent it from being successful against any real-world targets.
Why ZionSiphon Malware Matters
ZionSiphon Malware has been recently discovered in terms of "a significant advancement" in OT attack methods.
Although discovered ZionSiphon was not functional because it contained a critical validation error, it indicates that OT and utilities are in the crosshairs of lower sophistication actors seeking to build tools that can result in physical world consequences, such as the following:
1. Water infrastructure (desalination plants specifically) is a very high consequence target.
2. ZionSiphon has an intent to change course from cyber disruption (e.g., data loss and service degradation) to cyber-physical sabotage.
3. Security researchers view ZionSiphon as the prototype of future iterations of the proof-of-concept capable of becoming a more lethal weapon.
Defensive Recommendations Against ZionSiphon Malware
Organizations with critical infrastructure should take the following measures to enhance their defenses against threats like ZionSiphon malware.
1. Completely separate IT from OT networks
2. Monitor and restrict USB device usage in OT environments.
3. Create behavioral anomaly detection for OT systems.
4. Implement very tight patching and configuration management.
5. Use air gap technology or very strict access controls wherever possible.
For general enterprises, USB-borne threats must continue to be monitored as much of the initial access occurs in the IT layer, then pivots to OT.
Conclusion
The ZionSiphon malware was created to target municipal water treatment systems with a political objective. It can be inferred from Darktrace's detection of this malware (April 2026) that cyber-physical attacks are becoming a common threat and that AI is capable of detecting threats or possible threats (using behavioral methods).
At this time, there are certain deficiencies in the current version of ZionSiphon that would prohibit successful operation. However, both defenders and attackers will continue to be affected by the growth of OT malware with functional capabilities.
Therefore, visible defense capabilities, segregation of systems and data, and rapid response to any occurrence should be the priorities of those responsible for the protection of critical infrastructure.
FAQ Section
Q1: What is ZionSiphon malware?
ZionSiphon is an operational technology (OT) targeted malware, aimed at Altering Chlorine Levels by Changing the Pressure Settings in Water Treatment and Desalination Facilities
Q2: Why was ZionSiphon Malware discovered by Darktrace?
Darktrace's Behavioral Detection Platform Powered by AI Found Unusual Activity based on Combining IT Propagation with OT Sabotage Attempts
Q3: Is ZionSiphon Malware Active and a Threat to Organizations?
The Sample Analyzed was Inactive Because of Code Errors, but Represents an Obvious Future Development to Create More Dangerous Versions of the Malware
Q4: What Types of Systems Are Targets of ZionSiphon Malware?
Israeli Water Treatment and Desalination Facilities and Certain File Configuration Types Will be Targeted by ZionSiphon Malware Based on Pre-Configured Static IP Addresses of the Water Treatment and Desalination Facilities
Q5: How to Prevent Organizations from Becoming Victim of ZionSiphon Malware?
Network Segmentation, USB Usage Restrictions in OT Environments, Implementing Behavioral Monitoring, and Maintaining Strict Configuration Control Will Keep Organizations Safe from ZionSiphon Malware.